Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124

SolarWinds SERV-U 15.5.0.107 is an advanced and secure FTP, FTPS, SFTP, and HTTP/S server designed to help organizations securely transfer files over the internet or internal networks. SolarWinds SERV-U simplifies the process of managing file transfers and enables secure, efficient…

Kerio Control 9.4.5 build 8526 is a next-generation unified threat management (UTM) firewall designed for small to mid-sized businesses. It provides comprehensive network protection with an intuitive web-based interface. Whether you’re setting it up on a physical server, in VMware,…

Symantec Endpoint Protection Manager

Description The New Cybersecurity for Beginners and Dummies: Extensive Guide To Getting Started In Cybersecurity by Dr. Patrick Jeff is a comprehensive and easy-to-follow guide designed for beginners who want to dive into the world of cybersecurity. Whether you’re a…
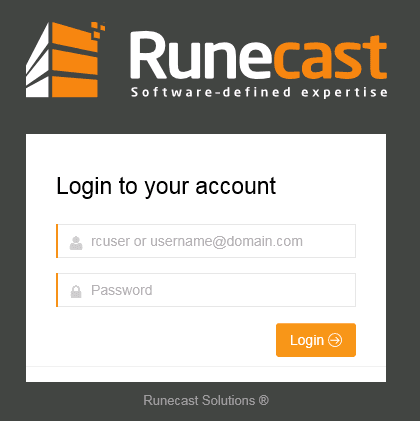
Runecast Analyzer is a powerful tool designed for proactive monitoring and management of VMware environments. It helps organizations ensure the health and compliance of their VMware vSphere infrastructure by scanning for configuration issues, security vulnerabilities, best practice violations, and hardware…

The book CISSP: 4 in 1 by Daniel Jones is an all-encompassing guide tailored for both beginners and experienced professionals aiming to achieve the Certified Information Systems Security Professional (CISSP) certification. This resource consolidates critical topics into a structured approach,…

The CISSP Cert Guide, Fourth Edition by Robin Abernathy and Darren R. Hayes is an essential resource for aspiring Certified Information Systems Security Professionals (CISSP). Designed to align with the latest exam objectives, this comprehensive guide equips readers with the…

The book Ultimate Splunk for Cybersecurity: Practical Strategies for SIEM Using Splunk’s Enterprise Security (ES) for Threat Detection, Forensic Investigation, and Cloud Security by Jit Sinha offers comprehensive insights into using Splunk for cybersecurity. This guide focuses on practical strategies…
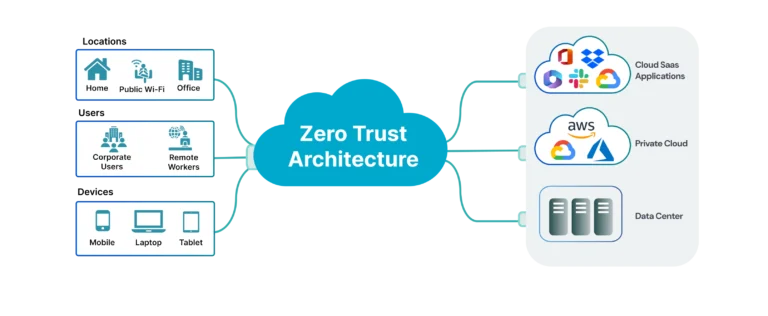
Zero Trust Architecture (ZTA) is a security model that operates on the principle of “Never trust, always verify”. This means that no user, device, or network is trusted by default, even if it’s within your network perimeter. In a private…
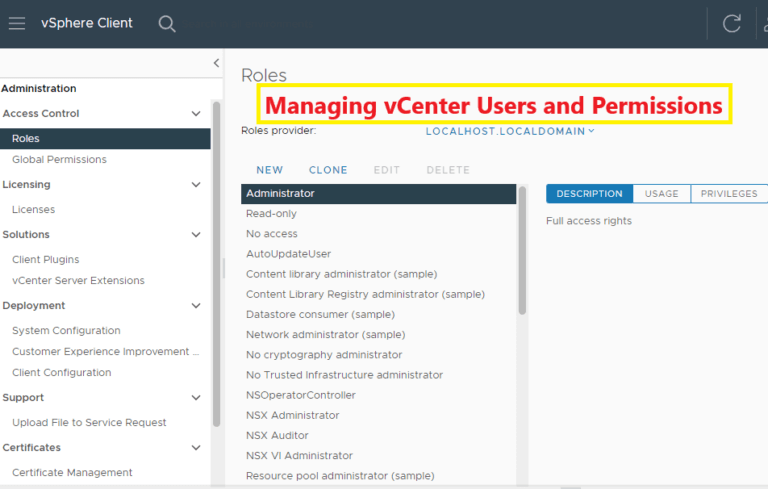
Managing users and permissions in VMware vCenter is a critical aspect of securing your virtual environment. With vCenter’s robust Role-Based Access Control (RBAC) model, you can define and enforce access controls, ensuring users have appropriate privileges without compromising security. This…