Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124

Kerio Control 9.4.5 build 8526 is a next-generation unified threat management (UTM) firewall designed for small to mid-sized businesses. It provides comprehensive network protection with an intuitive web-based interface. Whether you’re setting it up on a physical server, in VMware,…
ManageEngine Endpoint Central 11.4.2504.1 (formerly Desktop Central) is a unified endpoint management (UEM) solution trusted by thousands of IT teams worldwide. It helps you manage servers, desktops, laptops, and mobile devices from a central location. Whether you’re working in an…

Symantec Endpoint Protection Manager
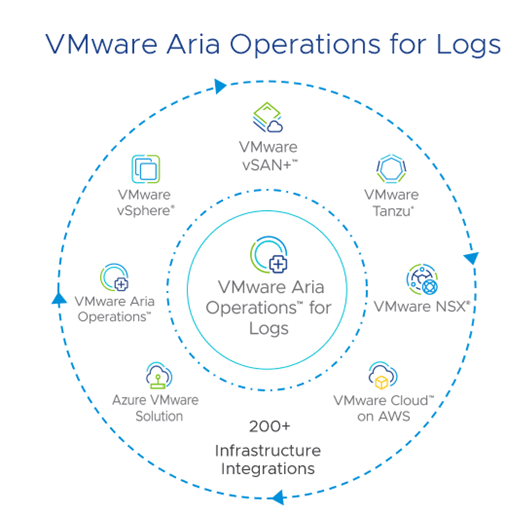
VMware Aria Operations for Logs 8.18 is a comprehensive log management solution designed to enhance real-time and archived log analysis, particularly within VMware environments. It leverages machine learning to facilitate intelligent grouping and high-performance search capabilities, enabling efficient troubleshooting across…

Microsoft has recently released a new version of its flagship productivity suite, Microsoft Office. You’ve likely noticed the ongoing shift in the IT industry toward SaaS solutions. To address this, Microsoft introduced Office 365 (now Microsoft 365) with a subscription…

In the ever-evolving world of IT security, password management remains one of the most crucial aspects of safeguarding user access to corporate systems. ManageEngine ADSelfService Plus, a popular self-service password management solution, has recently rolled out its new update —…

Microsoft released its new version of Windows 11, Windows 11 24H2, earlier this month. As usual, we will receive the installation discs of this operating system from Microsoft and share them with you without any interference and under the original…

Microsoft has released a new LTSC version of its Windows operating system, three years after the previous one. This new version is based on Windows 11, specifically Windows 11 24H2. We’ve discussed LTSC and its uses in previous posts, so…
vSphere 7 is a product of VMware that is used for very large, high-level tasks that involve setting up a cloud and cloud system. vSphere is designed to support the widest range of virtual infrastructure needs, with a wide range of enterprises, small and medium-sized…

Omnissa Horizon 8 delivers Windows desktops and applications virtually, as well as Linux desktops, to almost any end device, in a range of form factors from vSphere-based data centers. With clients for Microsoft Windows, Apple macOS, Linux, various mobile devices, and web browsers,…