Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Beyond the Perimeter: Auditing Active Directory Security with ADPulse’s 35-Point Automated Scan BEYOND THE PERIMETER ACTIVE DIRECTORY SECURITY AUDIT How ADPulse’s 35-point automated scan turns hours of manual AD auditing into minutes — and what those checks actually find inside…

The open-source remote access platform Pangolin has introduced version 1.16, bringing several enhancements focused on identity-driven access and platform usability. One of the headline additions is a new SSH authentication daemon that ties SSH access directly to the platform’s identity…
Wireshark, the widely used open-source tool for packet capture and network analysis, has released version 4.6.4, bringing a mix of security patches, stability fixes, and performance improvements. This update resolves three vulnerabilities (CVE-2026-3201, CVE-2026-3202, and CVE-2026-3203). The fixes address a…
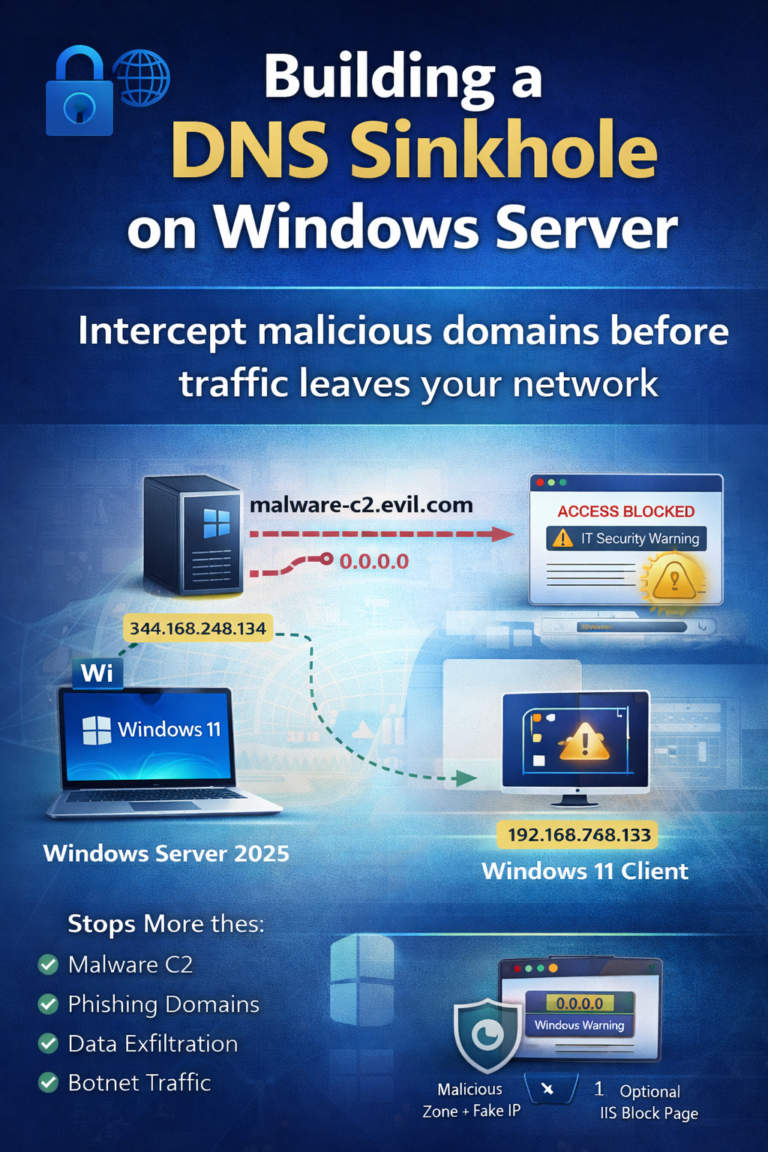
A DNS Sinkhole (also called a DNS blackhole or DNS blacklist) is a cybersecurity mechanism that intercepts DNS queries for known malicious, unwanted, or restricted domain names and redirects them to a controlled IP address — instead of resolving them…

Let’s Encrypt has introduced support for a new ACME challenge type called DNS-PERSIST-01, designed to simplify certificate issuance and renewal through a persistent DNS-based authorization model. This new mechanism, based on an IETF draft, serves as an alternative to the…
Web applications are one of the most targeted attack surfaces in modern infrastructure. Whether you’re running internal business portals, SaaS applications, or public-facing APIs, continuous vulnerability scanning is no longer optional. Acunetix Web Vulnerability Scanner is a commercial web application…
Organizations moving toward virtual infrastructure still need strong perimeter and internal network protection. The PA-VM-ESX-11.0.0 OVA provides a ready-to-deploy virtual firewall appliance from Palo Alto Networks designed for use in VMware environments. This appliance allows administrators, security engineers, and lab…
Veeam Backup & Replication version 13 (for Linux Appliance and Windows) includes significant improvements in malware detection compared to version 12.3, and several new features have been added. The different malware detection methods in this version, although different in function and…

A serious security concern is dominating virtualization news this month as a critical flaw affecting VMware ESXi servers has begun seeing active exploitation in the wild. System administrators and IT security teams need to act immediately to protect their infrastructure.…
Overview The widely used Linux networking service NetworkManager has introduced version 1.56, bringing a mix of functional improvements, policy refinements, and infrastructure updates aimed at both desktop and enterprise deployments. Released six months after NetworkManager 1.54, this latest version demonstrates…