introduction
Automating updates is a highly effective approach for managing Linux system updates. Employing automation tools, such as Ansible, ensures a consistent and regular application of updates, especially in environments with multiple Ubuntu servers. Utilizing Ansible streamlines the process of installing the latest updates and security patches on remote server environments, ensuring the system stays up-to-date with the latest features and protections.
What is Ansible?
Ansible stands out as a widely embraced, user-friendly, and agent-free configuration management tool within the DevOps realm, making it a popular choice for performing configuration tasks on targets.
It has the capability to install software, work with your package manager, update applications, modify files, adjust operating system service configurations, and perform various tasks. Ansible is frequently employed by developers and DevOps experts, often in conjunction with tools such as Terraform, to create comprehensive development environments.
Installing the Ansible control node
To utilize Ansible, it’s essential to have a Linux environment configured as your Ansible manager node. If you lack a dedicated Linux setup, you can conveniently employ options such as Windows Subsystem for Linux (WSL) within a Windows environment. Additionally, creating a straightforward solution like an LXC container in Proxmox is also a viable choice.
The device responsible for managing Ansible operations, encompassing machines, environments, and containers, is referred to as the Ansible control node. To initiate the process, installing Ansible on the control node, which serves as the central hub for managing Ubuntu servers, requires running the command sudo apt install ansible in the terminal of a Debian-based system such as Ubuntu.
This instruction installs Ansible, making sure you have both the core Ansible and essential modules ready for use. Additionally, please note that you may need to fulfill certain prerequisites, such as installing the “software-properties-common” deb package with the command: apt install software-properties-common.
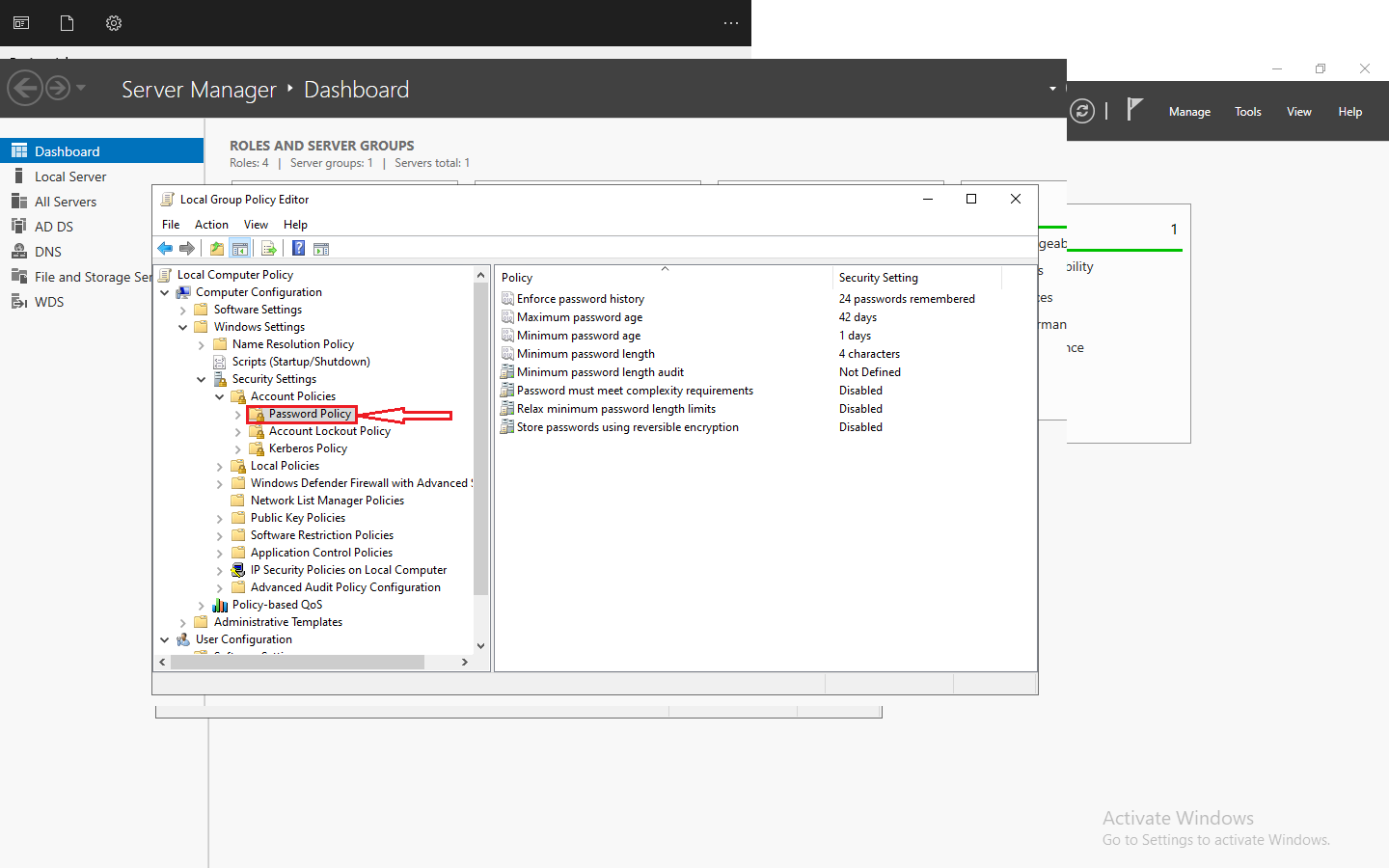
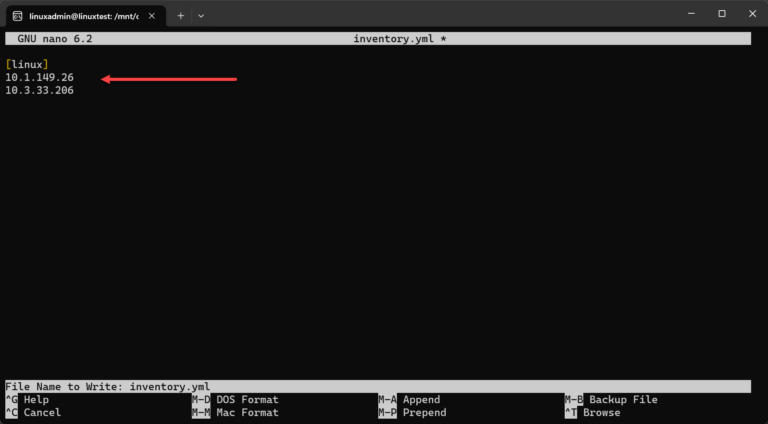
Configuring the Inventory File
Once installed, you must specify your remote servers in the Ansible inventory file by listing the IP addresses or hostnames of the Ubuntu servers you intend to oversee. The Ansible inventory file, formatted in YAML, serves as a record detailing the group of resources you aim to access along with their respective hostnames or IP addresses.
Handling authentication to Ubuntu remote servers
One of the configuration hurdles we must address involves authentication. When attempting to execute an Ansible playbook on Ubuntu servers, default settings often result in authentication issues, such as encountering missing sudo password or authentication failures.
Using SSH public key authentication is a simpler approach than trying to utilize an SSH password when connecting to your remote Ubuntu servers.
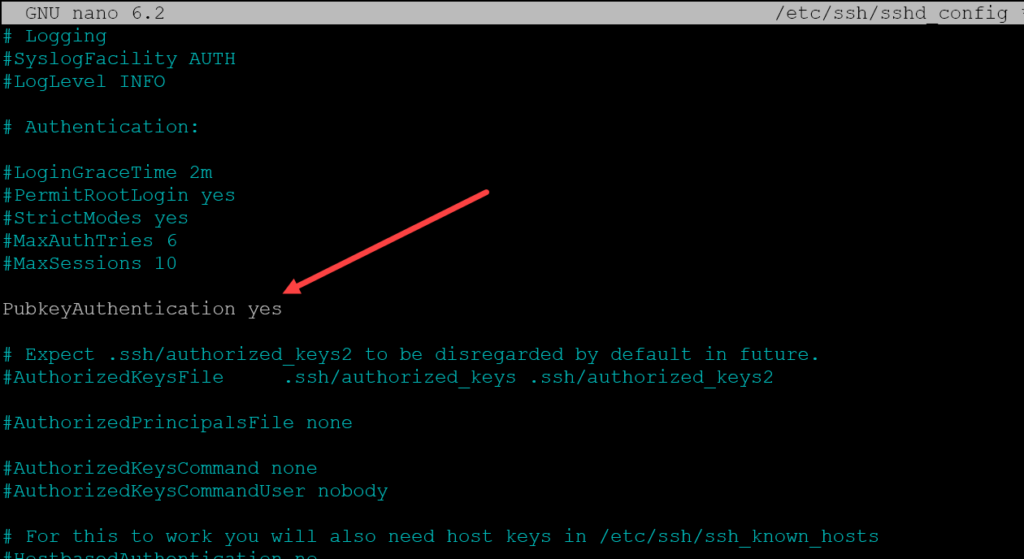
Configure public key authentication on your Ubuntu servers
To activate SSH public key authentication on your Ubuntu instances, go to the following file: /etc/ssh/sshd_config. Ensure that the specified line is uncommented and set to “yes”: PubkeyAuthentication yes.
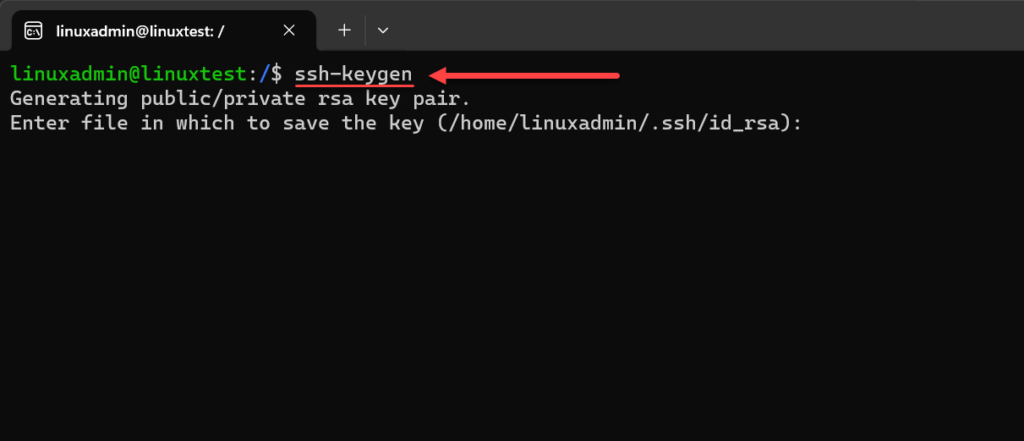
Generating an SSH keypair and copying the keypair to your Ubuntu server
Ensure that the user setup on your Ansible control node matches the user setup on your target Ubuntu servers. In my case, I’m using the user “linuxadmin.” After creating this user (it can be any user you prefer, not necessarily linuxadmin), generate your SSH key pair by running the command: ssh-keygen.
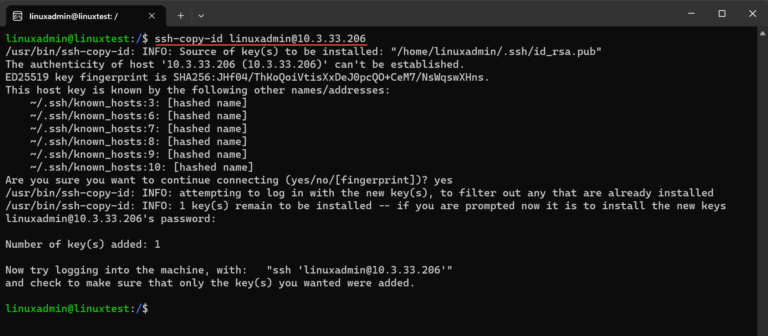
We’ll employ the ssh-copy-id command on our Ansible control node to transfer the public key segment of our key pair to the specified Ubuntu server.
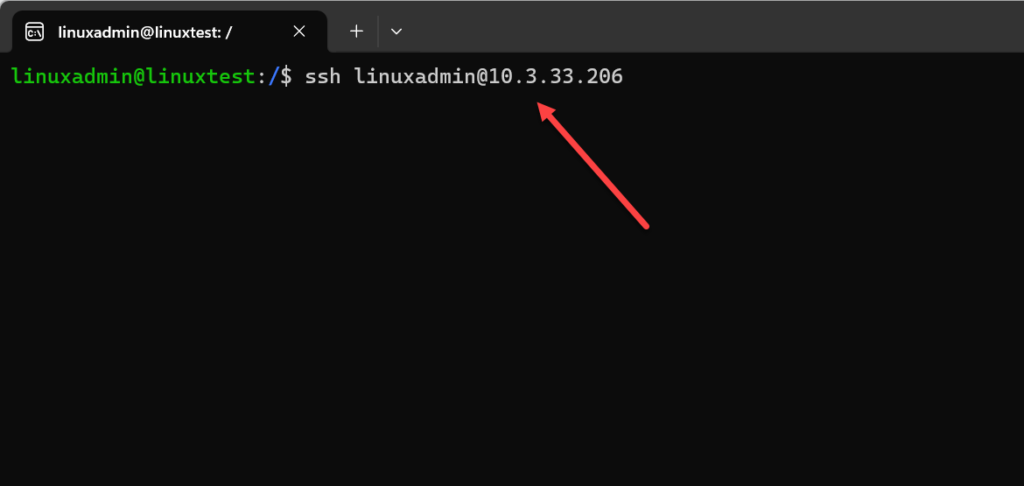
Test your connection
By now, you should be able to establish an SSH connection to your designated Ubuntu server without requiring a password. Utilize the provided syntax to connect from your Ansible control node: ssh <username>@<IP or hostname>.
Ansible Playbook to update Ubuntu
An Ansible playbook serves as a YAML file outlining automation tasks. When updating Ubuntu, the playbook utilizes the apt module, which handles apt packages on Debian-based systems.
— – hosts: all vars: ansible_host_key_checking: false become: true tasks: – name: Update and upgrade apt packages apt: update_cache: yes upgrade: yes
This playbook refreshes the apt cache, updates all packages to their latest versions using commands such as sudo apt get update and sudo apt get upgrade. Additionally, it employs the update_cache: yes stanza to update the package cache and concludes with an apt get dist upgrade in the final code block.
Verify the accuracy of your package installation by consistently reviewing the information details in the specified path locations on your remote host.
/etc/apt/sources.list
/etc/apt/sources.list.d/
Install only selective Ubuntu updates
Ansible tags provide increased control by enabling the execution of particular tasks within your playbook, allowing for targeted updates. An example usage could be as follows.
—- hosts: allbecome: truetasks:- name: Update the repository cacheapt:update_cache: yescache_valid_time: 3600- name: Install only security updatesapt:upgrade: ‘dist’update_cache: yesforce_apt_get: yesdefault_release: “{{ ansible_distribution_release }}-security”
Running the Playbook on Remote Servers
Now that we have the Ansible control node configured,
To execute the playbook and update your remote servers, use:
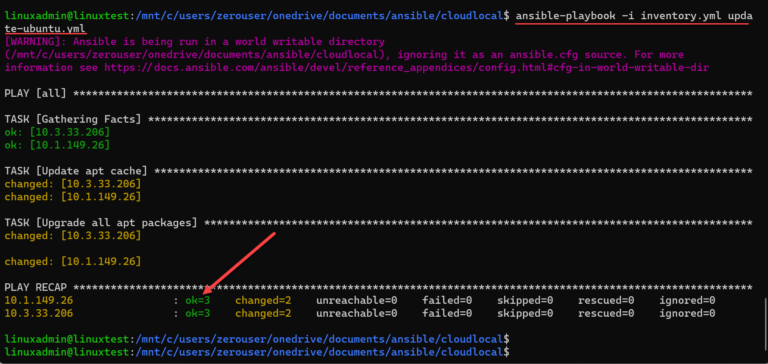
ansible-playbook -i inventory.yml update-ubuntu.yml
This directive executes tasks on all servers specified in your inventory file. As demonstrated below, the directive is executed, and Ansible proceeds to collect information, refresh the apt cache, and upgrade all apt packages.
We observe the playbook summary indicating that both hosts are in an OK status, confirming that the hosts were successfully modified according to the playbook. Take note of any errors or warnings in the playbook outcomes.
Handling Common Challenges
You might encounter difficulties connecting to your Ubuntu servers, often related to authentication problems. If you’re not utilizing public key authentication, you could encounter a message indicating a missing sudo password.
Dealing with Missing sudo Passwords
If your remote servers need a sudo password, include the -K flag in your playbook command along with your sudo user. This will prompt you for the sudo password while the playbook is running.
Errors connecting
Ensure that your Ansible control node can establish a reliable connection with the designated Ubuntu servers, covering SSH access on port 22. It might be necessary to incorporate firewall exceptions on the Ubuntu server or any intermediary firewall devices positioned between the Ansible control node and the specified Ubuntu servers.
For UFW on the Ubuntu side, you can run the following command:sudo ufw allow ssh.
GUI version of Ansible with Scheduling
If you seek a user-friendly interface for Ansible with scheduling and Git integration, Ansible Semaphore stands out as an excellent choice. This free and open-source tool offers a smooth GUI, enabling effortless scheduling of Ansible playbook runs and seamless integration with your Git code repository.
You can create various users with specific privileges for role-based access control. Explore my guide on utilizing Ansible Semaphore, a fantastic open-source GUI for Ansible.