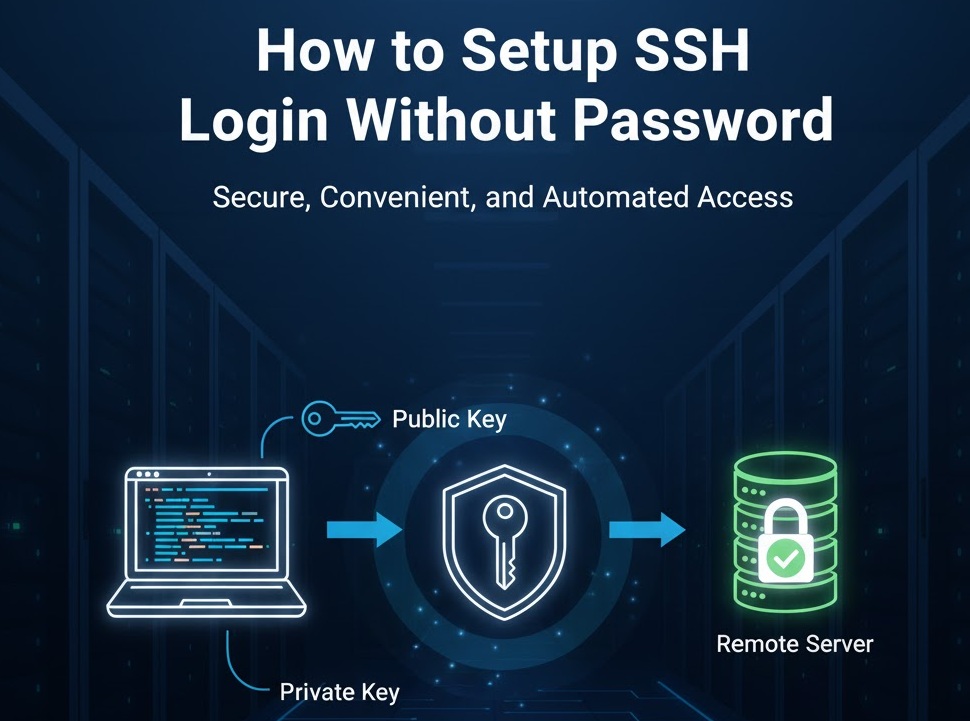
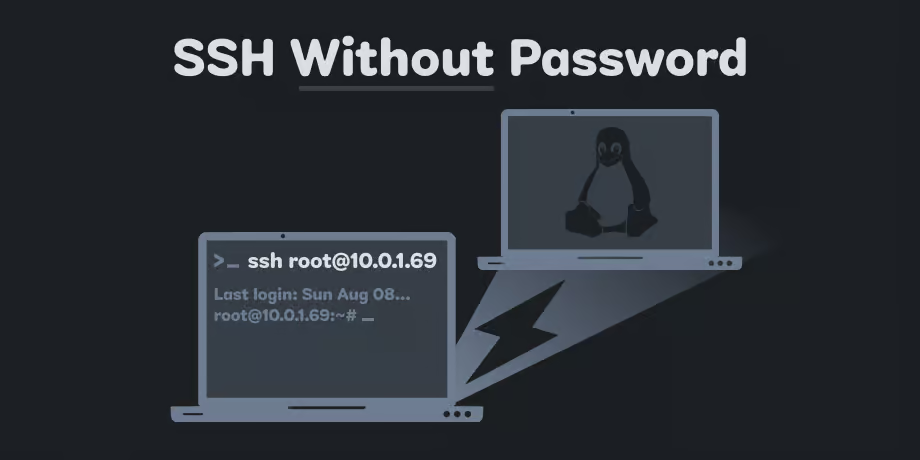
How to Setup SSH Login Without Password
SSH is used for logging into servers to run the commands and programs remotely. However, sometimes you might want or...
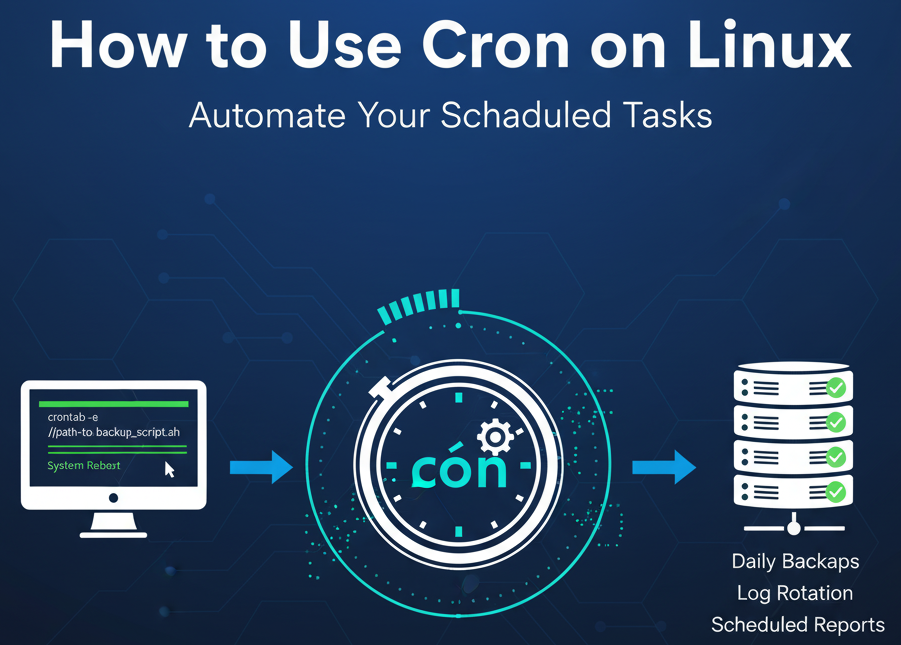
How to Use Cron on Linux: Tips, Tricks, and Examples
What is Cron?How Cron WorksCron Files and DirectoriesUser CrontabsSystem-Wide CrontabCron’s DirectoriesCron Syntax BasicsMinute (0-59)Hour (0-23)Day of Month (1-31)Month (1-12)Day of...
SSH to Port Other Than 22: How to Do It (with Examples)
By default, the SSH server runs on port 22. However, there are occasions when it is run in a different...
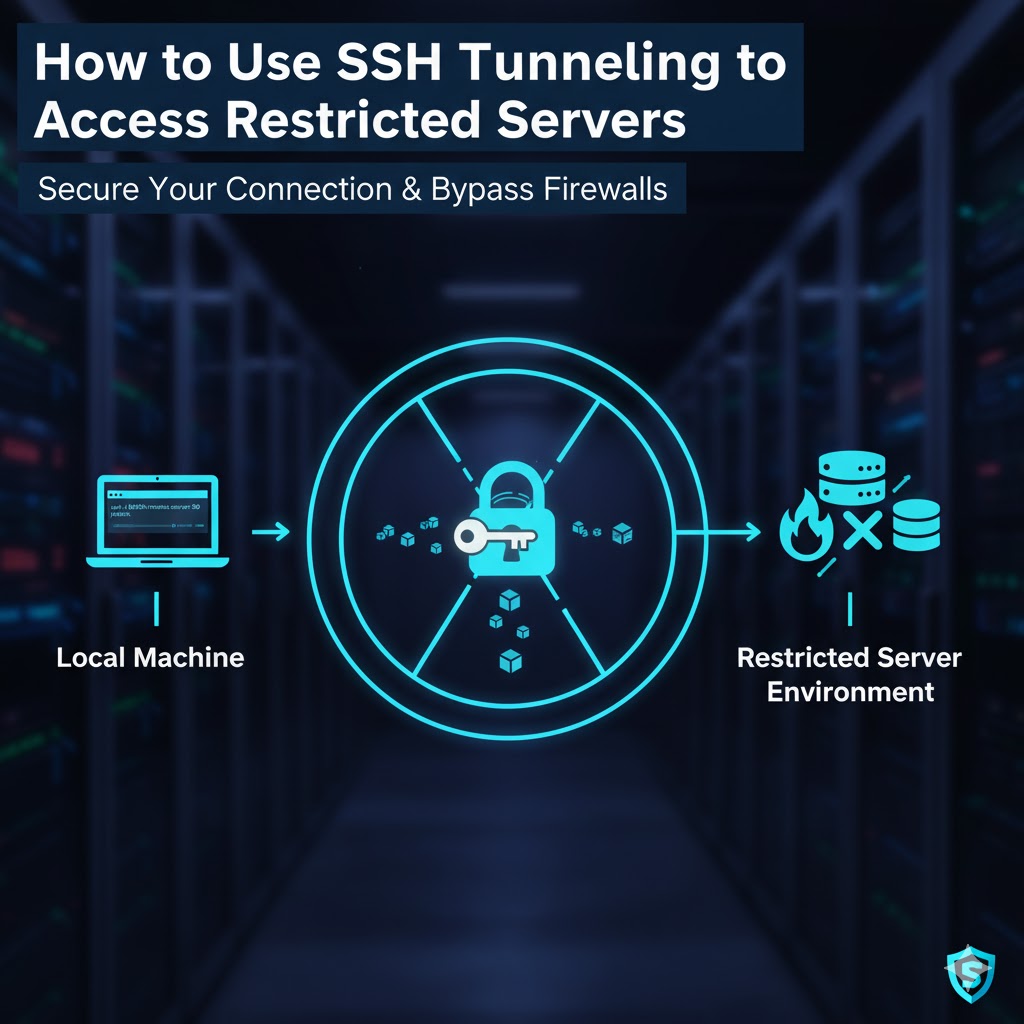
How to Use SSH Tunneling to Access Restricted Servers
SSH tunneling or SSH port forwarding is a method of creating an encrypted SSH connection between a client and a...
How to Setup SSH Login Without Password
SSH is used for logging into servers to run the commands and programs remotely. However, sometimes you might want or...
How to Generate an SSH Key Pair (with Examples)
Password authentication is the default method most SSH clients use to authenticate with remote servers, but it suffers from potential...
How to Set Up SSH to Use Two-Factor Authentication
Secure Shell (SSH), a protocol widely used for secure remote login from one computer to another, offers robust encryption to...
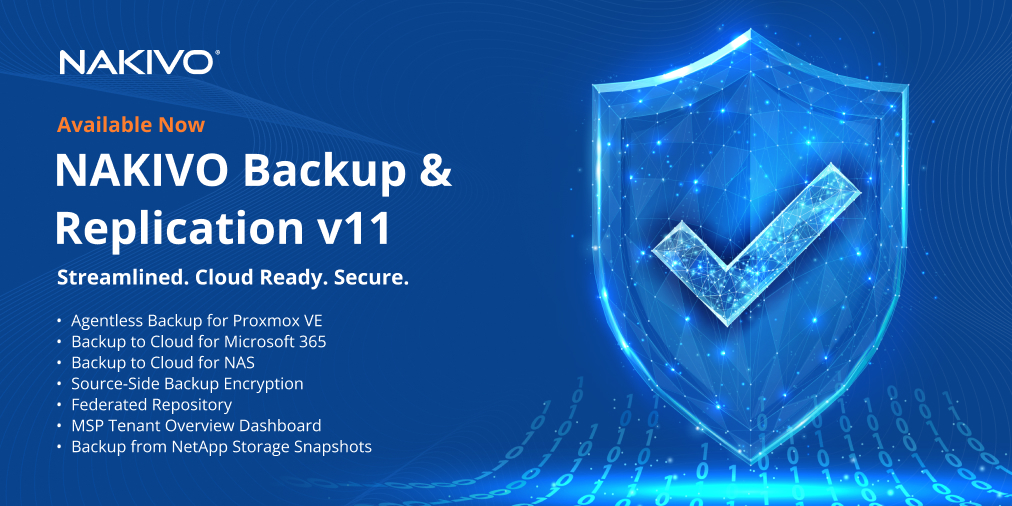
NAKIVO Backup & Replication v11.1.0
In today’s IT world, data protection is not just a necessity—it’s a critical part of business continuity. With the growing...
How to Secure SSH Server with SSHGuard: A Practical Guide
What’s SSHGuard?SSHGuard vs Fail2Ban: Key DifferencesDefault Services Monitored:Ease of Configuration:Installing SSHGuard on LinuxFedoraConfigure SSHGuardSSHGuard Configuration When Using UFW/nftablesSSHGuard Configuration When...
How to Get Notified on SSH Logins on Linux
Knowing who and when logs to your Linux server via SSH is always a good idea. Even if you’re the...