Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124

VMware Aria is essentially a trusted and proven software solution that empowers IT managers with the tools they need to manage operational processes across virtual, physical, cloud, and other environments. VMware Aria can be deployed using a management cluster and…

VMware Aria Suite provides a comprehensive solution for deploying, configuring, managing, and upgrading VMware Aria Suite products. These products include VMware Aria Operations, VMware Aria Automation, VMware Aria Automation Orchestrator, VMware Aria Operations for Networks, and VMware Aria Operations for…

VMware Aria Operations (formerly VMware vRealize Network Insight) enables IT organizations to create a modern platform for on-premises and virtual infrastructure automation. This enables operations and management based on modeling security and firewall rules, and to see how network segmentation…
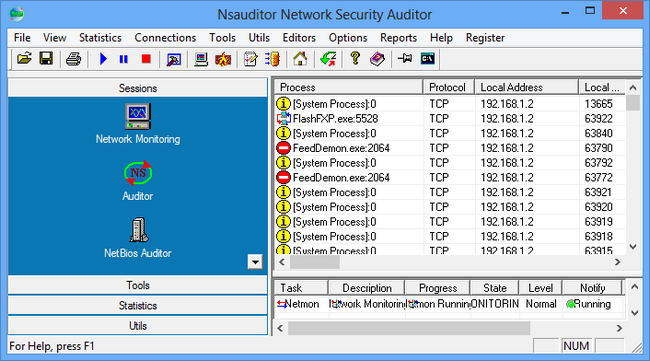
Overview of Nsauditor Network Security Auditor 3 Benefits Nsauditor is a complete networking software package that includes more than 45 network tools and utilities for network auditing, scanning, network connections monitoring, and more. It combines Network Security and Vulnerability Scanning,…

Overview of RecoveryTools Kerio Migrator This is an advanced tool to Convert Kerio Emails, Contacts, and Calendars. It migrates all your Kerio Mail Server data, including emails, attachments, contacts, calendars, tasks, notes, etc. Features of RecoveryTools Kerio Migrator Technical Details…

What you’ll learn DISCLAIMER-This course is strictly for educational purposes and does not support any illegal activities. Participants are expected to use the knowledge responsibly, within legal and ethical boundaries. Completion of the course does not guarantee success in the…

What you’ll learn Requirements Basic computer skills (e.g., installing applications and navigating an operating system) Description Welcome to Mastering Ethical Hacking: From Basics to Advanced Techniques, a comprehensive journey into the world of cybersecurity and ethical hacking, designed for beginners…

What you’ll learn Experience the epitome of professionalism with AGT (AllGoodTutorials), your premier destination for exclusive online courses across a diverse spectrum of fields. Whether you’re delving into programming, cybersecurity, design, or beyond, AGT stands as a beacon of excellence…

What you’ll learn John Christopher is a Technical Instructor that has been in the business for 25 years. His first experience with information technology occurred in the early 90s when he ran an MS-DOS based BBS(Bulletin Board System) as a…

What you’ll learn Kashif is an IT Professional with over a decade of experience working for several fortune 500 companies in the US market. He has utilized his technical skills for companies such as Pfizer, Verizon, Cox communications and IBM.…