Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124

Canonical has confirmed on x that its Ubuntu web infrastructure is currently dealing with a sustained cross-border distributed denial-of-service (DDoS) attack, leading to disruptions across public-facing services.
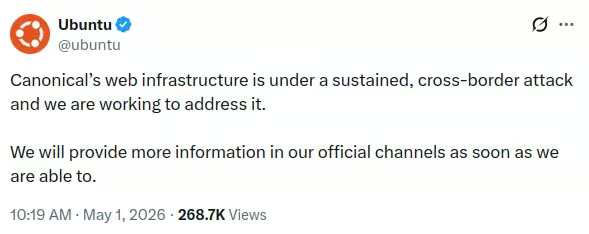
In an official announcement on Ubuntu Discourse, the company stated that it is actively working to mitigate the issue. However, it has not shared technical specifics, identified any attackers, or provided a timeline for full recovery.
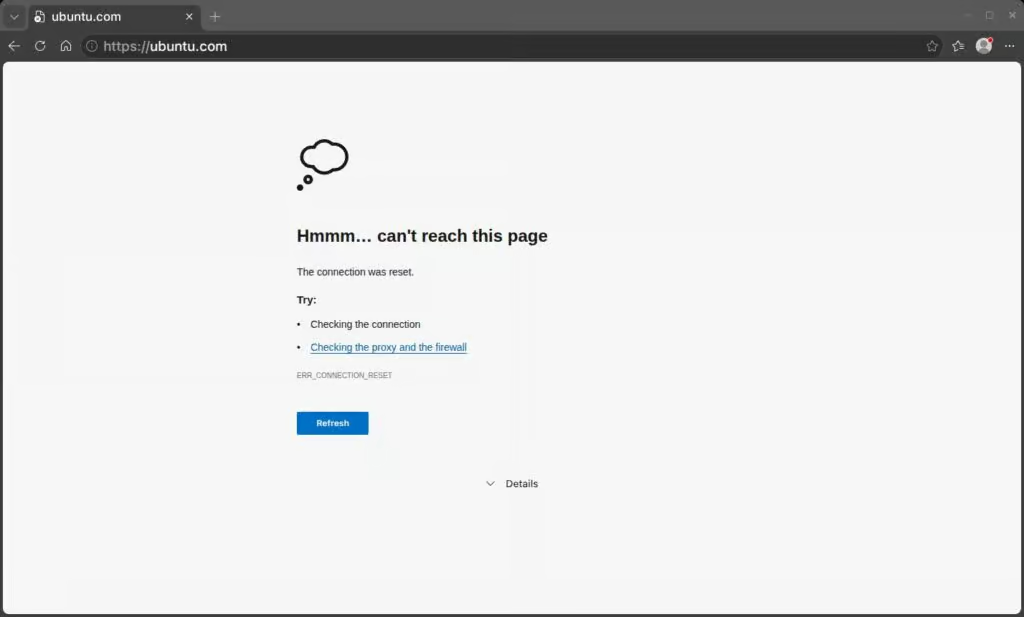
As a result, users have reported slow loading times and intermittent outages on Ubuntu-related websites, including ubuntu.com and associated services. Canonical’s status page also reflects ongoing incidents affecting both Ubuntu and Canonical infrastructure.
It’s important to note that a DDoS attack does not imply a system breach. These attacks typically work by overwhelming servers with large volumes of traffic, making services slow or temporarily unavailable rather than compromising data or systems.
This incident follows a similar disruption in August 2025, when Arch Linux reported a DDoS attack impacting its website, the Arch User Repository, and forums. In that case, the issue primarily affected availability, not package integrity.
The Ubuntu disruption highlights a broader pattern of availability-focused attacks targeting Linux distribution infrastructure. While some external reports have speculated about possible responsibility, Canonical has not attributed the attack to any specific group. For now, the confirmed details remain limited to an ongoing DDoS attack affecting its web services.