Block Program Installations from USB Drives on Domain Computers Using Group Policy in Windows Server 2025
Introduction
USB drives are everywhere — and that is precisely the problem. In a managed domain environment, an uncontrolled USB port is an open door for unauthorized software installations, malware delivery, data exfiltration, and licensing headaches. One employee plugging in a personal flash drive loaded with an unsigned installer can quietly bypass your entire software deployment policy in under a minute.
The silver lining is that Windows Server 2025 and its Group Policy engine give you a powerful, built-in mechanism to shut this down completely — no third-party endpoint agents required. By combining Device Installation restrictions with Windows Installer policies through the Group Policy Management Console (GPMC), you can prevent domain computers from running or installing any software originating from removable storage, domain-wide, from a single configuration point.
This guide walks you through every step of that process, with clear explanations of what each policy does and why it matters for your environment.
Why Blocking USB-Based Installs Is Non-Negotiable in 2025
USB-based threats have evolved far beyond the classic autorun worm. Today’s risks include:
- Malware Delivery Vectors: Attackers frequently preload USB drives with trojanized installers that appear legitimate. Once a user double-clicks that setup.exe, traditional antivirus often has a narrow window to intervene — especially with zero-day payloads.
- Shadow IT and Licensing Risk: Employees installing unapproved tools from personal drives creates untracked software sprawl, potential licensing violations, and configurations that your IT team knows nothing about.
- Data Exfiltration Risk: While this policy focuses on installs, blocking USB executables also limits the payload-drop phase of many data theft attack chains where malware is first deposited via removable media.
- Compliance and Audit Requirements: Frameworks like ISO 27001, NIST SP 800-53, and PCI-DSS explicitly require organizations to control removable media and unauthorized software. This GPO setting directly supports those controls.
- Endpoint Configuration Drift: Unauthorized software installations degrade standardized machine images and create support complexity. Blocking installs at source keeps every endpoint in a known, manageable state.
Understanding the Two-Layer Approach
Blocking USB installations effectively in Windows Server 2025 is not a single switch — it requires two complementary Group Policy layers working together:
| Layer | Policy Area | What It Does |
| Layer 1 | Device Installation Restrictions | Prevents removable storage devices from being used to run or install software at the hardware driver level. |
| Layer 2 | Windows Installer Controls | Blocks MSI and executable installers from running when launched from removable media, regardless of user privilege level. |
| Bonus Layer | Software Restriction Policies / AppLocker | Optional deeper enforcement — blocks execution of any binary from a USB drive path, even non-installer executables. |
Prerequisites
Before you begin, confirm you have the following in place:
- Windows Server 2025 domain controller with Active Directory Domain Services configured.
- Group Policy Management Console (GPMC) available on your admin workstation or DC.
- Domain Administrator credentials or delegated GPO management rights.
- An Organizational Unit (OU) containing the target computer accounts (not user accounts — this policy is Computer-based).
- At least one domain-joined Windows 10/11 test machine to validate the policy before broad rollout.
- A USB drive available for testing the restriction after deployment.
Step-by-Step Configuration Guide
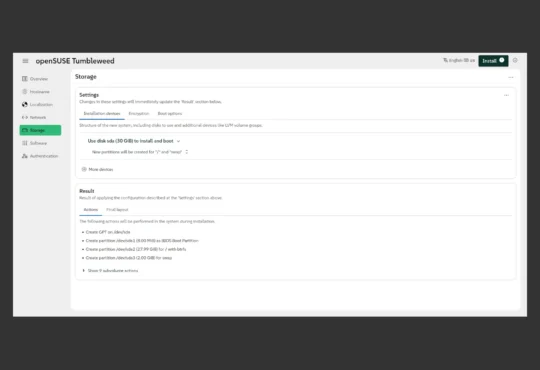
Step 1: Open Group Policy Management Console
Log in to your Windows Server 2025 domain controller or a management workstation with RSAT (Remote Server Administration Tools) installed. Press Windows + R, type gpmc.msc, and press Enter to launch the Group Policy Management Console.
In the left navigation tree, expand your forest, then your domain (e.g., vmorecloud.com), and locate the Organizational Unit that contains the computer accounts you want to protect.
Step 2: Create a New GPO Linked to the Computers OU
Right-click the target OU (for example, Domain Computers or Workstations) and select Create a GPO in this domain, and Link it here. Name it something clear and descriptive, such as
Block-USB-Program-Installations
Once created, right-click the new GPO and select Edit to open the Group Policy Management Editor.
IMPORTANT This policy targets Computer Configuration — not User Configuration. That means it enforces restrictions at the machine level regardless of which user logs in. Make sure your GPO is linked to an OU containing computer accounts, not user accounts.
Step 3: Block Removable Storage Device Installation
Inside the Group Policy Management Editor, navigate to:
Computer Configuration → Administrative Templates → System → Device Installation → Device Installation Restrictions
This section controls which types of hardware devices can be installed or used on the machine. Locate and enable the following two policies:
Policy A: Prevent installation of removable devices
Double-click this setting and set it to Enabled. This prevents Windows from installing drivers for any new removable storage devices — including USB drives not previously seen by the system — stopping them from becoming accessible as a drive letter.
Policy B: Prevent installation of devices not described by other policy settings
Also set this to Enabled. This acts as a catch-all — any device class not explicitly permitted by other policies will be blocked from installing. Combined with Policy A, this closes the gap for edge-case USB device types that could otherwise bypass the first restriction.
NOTE Already-installed USB storage devices on existing machines will remain accessible unless you also enable the policy: Prevent installation of devices using drivers that match these device setup classes — targeting the removable storage GUID {53f5630d-b6bf-11d0-94f2-00a0c91efb8b}. See the Advanced section at the end of this guide.
Step 4: Block Windows Installer Packages from Removable Media
Now navigate to the Windows Installer policy path:
Computer Configuration → Administrative Templates → Windows Components → Windows Installer
Locate the following setting:
Prevent removable media source for any install
Double-click it and set it to Enabled. This tells Windows Installer (msiexec.exe) to refuse any installation initiated from a removable drive path — including USB flash drives, external hard drives, and SD cards. Users will receive an error if they attempt to run an .msi installer from a USB source.
Step 5: Block AutoPlay to Prevent Silent Executions
Even with the above policies in place, AutoPlay can silently trigger executable content when a USB drive is connected. Navigate to
Computer Configuration → Administrative Templates → Windows Components → AutoPlay Policies
Enable both of the following settings:
- Turn off AutoPlay — Set to Enabled and apply it to All Drives. This prevents Windows from automatically launching any content when a drive is connected.
- Set the default behavior for AutoRun — Set to Enabled and configure it to Do not execute any autorun commands. This suppresses autorun.inf-based execution attempts.
Step 6: Force Group Policy Update and Verify
Save and close the Group Policy Management Editor. The policy will propagate automatically within the next 90-minute refresh cycle, but you can force an immediate update. Run the following on the domain controller:
gpupdate /force
On each target client machine (or via a remote PowerShell session):
gpupdate /force
To verify the policy was received and applied correctly on a client machine, run:
gpresult /r
Look for your GPO name under Computer Settings → Applied Group Policy Objects. If it appears there, the policy is active.
Step 7: Test the Restriction
Log in to a domain-joined test workstation as a standard domain user. Insert a USB drive that contains an installer file (.exe or .msi). Attempt to run the installer. You should encounter one of the following outcomes:
- The installer fails to launch with an error message stating the installation source is not accessible.
- If the USB drive itself is blocked at the device installation level, the drive may not appear as a recognized volume at all.
- AutoPlay prompts will not appear upon USB insertion if AutoPlay policies were applied correctly.
If any of these behaviors are not observed, review the troubleshooting section below before proceeding to a broader rollout.
Key Highlights at a Glance
| Policy / Setting | Value / Detail |
| GPO Node | Computer Configuration (machine-level enforcement) |
| Device Installation Path | System → Device Installation → Device Installation Restrictions |
| Windows Installer Path | Windows Components → Windows Installer |
| AutoPlay Path | Windows Components → AutoPlay Policies |
| Prevent Removable Devices | Enabled — blocks new USB device driver installs |
| Prevent Removable Media Install | Enabled — blocks MSI/EXE installers from USB source |
| Turn Off AutoPlay | Enabled for All Drives |
| Applies To | Domain computers in the linked OU |
| Requires Machine Reboot? | Recommended after initial deployment for Device Install policies |
| Verification Command | gpresult /r or gpresult /h report.html |
| Platform | Windows Server 2025 + Active Directory Domain Services |
| Does Not Affect | Network-based or SCCM/Intune software deployments |
Advanced: Block Already-Installed USB Devices by Device Class GUID
The Device Installation Restrictions policies above primarily block new USB storage devices from being installed. If users already have USB drives recognized by their machines, you need an additional step to prevent those existing devices from functioning.
In the Group Policy Management Editor, navigate to the same Device Installation Restrictions path and enable:
Prevent installation of devices using drivers that match these device setup classes
Click Show to add the following GUID, which represents the USB Mass Storage device class:
{53f5630d-b6bf-11d0-94f2-00a0c91efb8b}
You can also add the following GUID for all removable storage devices to cast a wider net:
{53f56307-b6bf-11d0-94f2-00a0c91efb8b}
Enable Also apply to matching devices that are already installed to ensure the policy applies retroactively to devices already recognized by the system. Note that a reboot is typically required for this setting to take full effect.
Conclusion
USB-based software installs represent one of the oldest and most persistent endpoint security gaps in managed Windows environments — and Windows Server 2025 Group Policy gives you everything you need to close it without spending a penny on third-party tools.
By layering Device Installation Restrictions, Windows Installer controls, and AutoPlay policies together under a single Computer Configuration GPO, you create a robust, multi-point defense that prevents unauthorized software from ever getting a foothold on your domain computers — regardless of who’s sitting at the keyboard.