Every day, following the release of numerous new vulnerabilities, attackers actively seek ways to exploit these vulnerabilities to further their malicious activities. Consequently, any delay in identifying and remedying software vulnerabilities provides attackers with ample opportunities to infiltrate and compromise vulnerable systems, gaining access to valuable information.
Consequently, without continuous scanning of assets and promptly addressing vulnerabilities, organizations face serious risks. The significance of vulnerability scanning is underscored by its inclusion in the list of 20 SANS security controls. The output from this security control, namely the scanner output, plays a pivotal role in the penetration testing phase. Therefore, the accuracy and precision of the scanner output significantly impact the effectiveness of penetration testing. The Nessus scanner, developed by the reputable Tenable company, is a notable option in this context. The Nessus scanner demonstrates the capability to identify and assess over 47,000 unique assets, including those from Cisco, Juniper, HP, F5, and others. Moreover, it encompasses various operating systems such as Windows, Linux, and Mac, as well as virtualization platforms like VMware, diverse software, and even drivers.
Nessus App Features
- Detection of bots and Trojans
- Support for various platforms
- Vulnerabilities in Passive Mode
- Ability to perform multiple scans at the same time
- Includes a tool to compare scan results
- High scanning speed
- Vulnerability Assessment
- Working with a variety of computer equipment
- Identify security weaknesses in local and remote networks
- Detecting the failure to install new updates on the system
- Simulating different attacks under different conditions
- And…
Examples of vulnerabilities and exposures Nessus can scan for include
- Vulnerabilities that could allow unauthorized control or access to sensitive data on a system.
- Misconfiguration (e.g. open mail relay, missing patches, etc.).
- Default passwords, a few common passwords, and blank/absent passwords on some system accounts. Nessus can also call Hydra (an external tool) to launch a dictionary attack.
- Denials of service vulnerabilities
Nessus scans encompass a broad spectrum of technologies, covering operating systems, network devices, hypervisors, databases, web servers, and critical infrastructure. The scan results can be presented in diverse formats, such as plain text, XML, HTML, and LaTeX. Additionally, these results can be stored in a knowledge base for debugging purposes. On UNIX systems, scanning can be automated using a command-line client. Various commercial, free, and open-source tools are available for managing individual or distributed Nessus scanners on both UNIX and Windows platforms.
Beyond assessing known network vulnerabilities, Nessus offers additional functionalities. For example, it can utilize Windows credentials to inspect patch levels on machines running the Windows operating system. Nessus is also capable of supporting configuration and compliance audits, SCADA audits, and PCI compliance assessments.
Download link Nessus SC 10.6.0 Update 20230830 + Crack
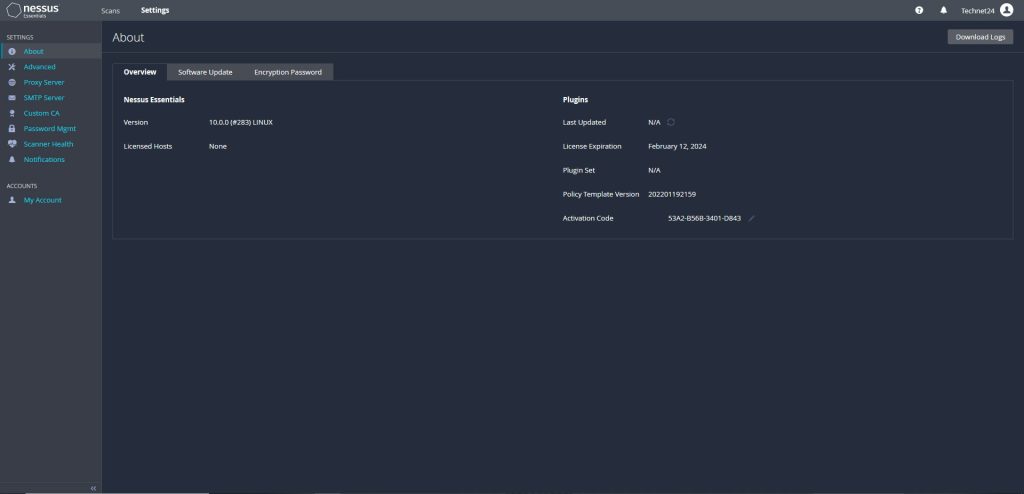
Download link Nessus SC Update 202201192159 virtual machine version
Download – Size : 500 MB
Nessus
Software Setup Training
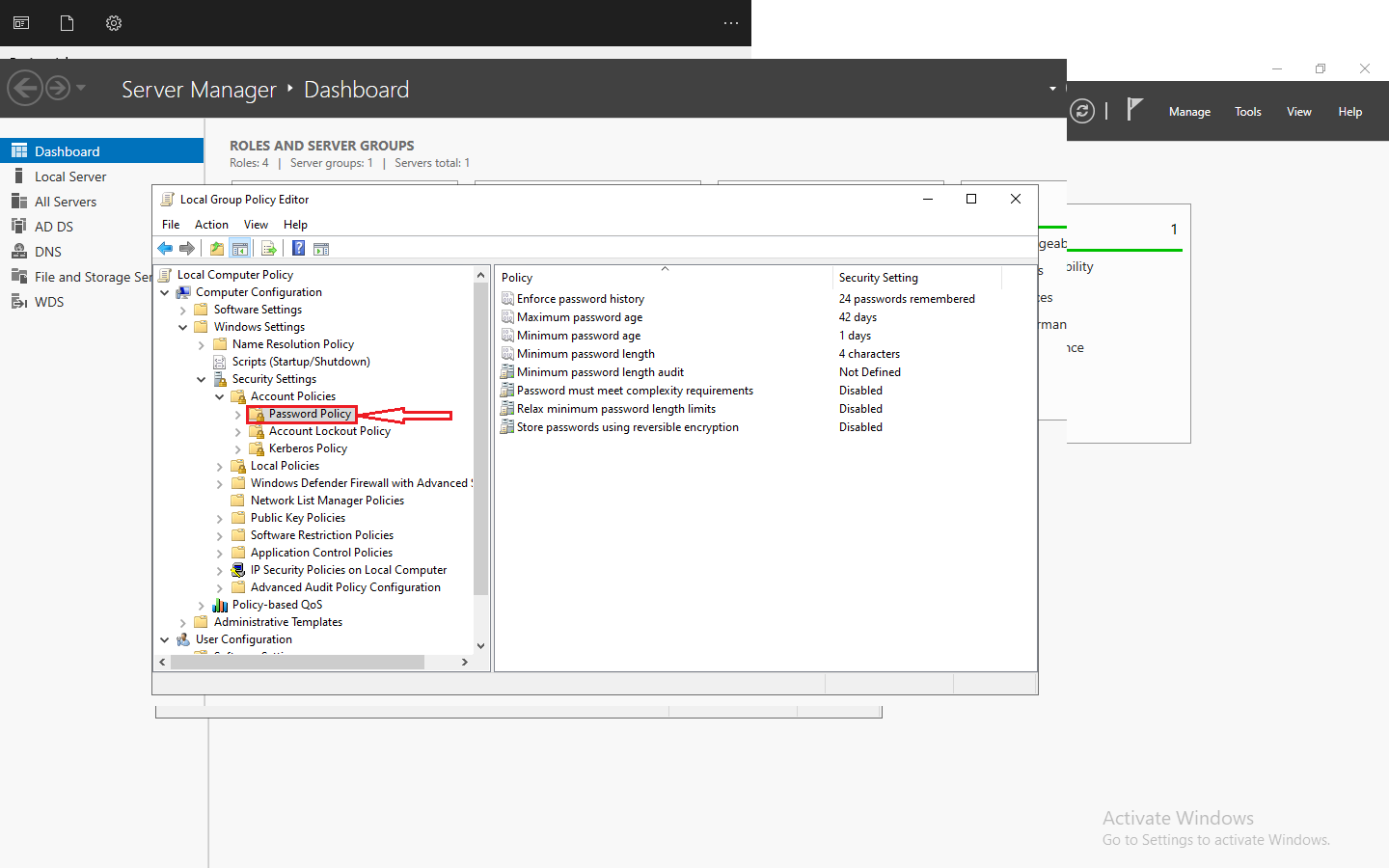
- To use the software you need VMware virtualizer.
- You can change the amount of RAM and CPU of the virtual machine according to the system specifications. (is optional)
- Login Specifications Virtual MachineUsername: root
Password: technet24Login profile to software
Username: Nessus
Password: technet24 - To find the internal IP address of the virtual machine, use ifconfig | more.
- After you find the internal IP address of the virtual machine on your main operating system, open your browser and go to https://IP:8834 address.
- Nessus software needs to prepare plug-ins and tools, and depending on the speed of your hardware, especially HDD/SSD, it may take anywhere from 20 to 60 minutes.
- At the end, enter by the username and password of the Nessus software, now you can use all the features of the software infinitely.
Size: 4.96 GB
Filename: technet24.ir