Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
The definitive guide to deploying, configuring, and securing Read-Only DNS on a Windows Server 2025 RODC — with real commands.
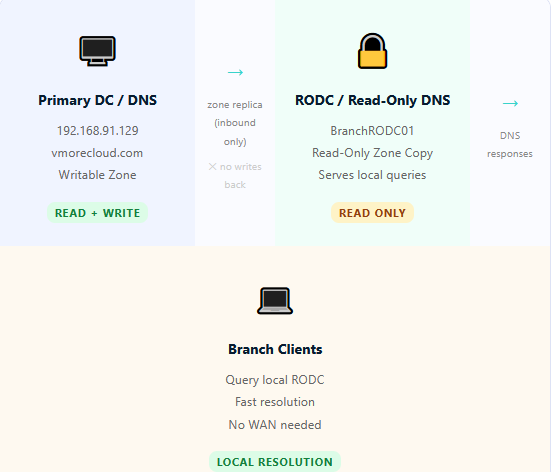
Read-Only DNS is the DNS Server role running on a Read-Only Domain Controller (RODC). It hosts a copy of your Active Directory-integrated DNS zones — but that copy is read-only. It answers queries, forwards requests it can’t resolve, and participates in the DNS infrastructure of your domain — but it cannot accept dynamic updates, cannot be used to modify zone data, and cannot propagate changes back into your AD forest.

Think of it as a DNS mirror with a one-way valve. Clients at the branch get fast, local DNS resolution. Zone data stays clean and controlled. And if the RODC is ever compromised, your DNS infrastructure remains intact because there was never anything writable to corrupt.
192.168.91.129 instead. Your zone data is never modified at the branch.
When you install the DNS Server role on an RODC, it behaves differently from DNS on a writable DC in three important ways:
The RODC receives a replicated, read-only copy of your AD-integrated DNS zones. This replica is pulled from the writable DC during standard AD replication. The RODC’s DNS service reads from this zone database to answer queries — but the DNS service itself has no write permission to the zone objects stored in AD.
When a client (like a workstation registering its A record) sends a dynamic DNS update to the RODC’s DNS server, the RODC doesn’t reject it outright with an error. Instead, it responds with a referral — pointing the client to the primary writable DNS server (192.168.91.129) to complete the update. The client retries against the correct server, and the update succeeds. From the end user’s perspective, DNS registration just works.
The Read-Only DNS server maintains its own local DNS resolver cache for external (internet) queries. This cache is populated through normal recursive resolution and serves future identical queries instantly without WAN traffic. This cache is local only — it does not replicate to other DCs.
Here’s what actually happens during a typical DNS lookup at a branch office with Read-Only DNS:
fileserver.vmorecloud.com).BranchRODC01.192.168.91.129.Windows Server 2025 brings meaningful refinements to how Read-Only DNS behaves compared to earlier server versions. Here’s what’s worth knowing:
| Feature / Behaviour | Standard DNS (Writable DC) | Read-Only DNS (RODC) |
|---|---|---|
| Zone data type | Read/Write AD-integrated | Read-only AD-integrated replica |
| Accepts dynamic updates? | Yes — directly | Redirects to primary DC |
| Can modify zone records? | Yes | No |
| Answers DNS queries? | Yes | Yes — from local cache + zone |
| Operates during WAN outage? | Yes | Yes — for cached + zone records |
| DNSSEC support (WS2025)? | Full signing + validation | Validation only (no signing) |
| DNS over TLS (DoT)? | Yes | Yes (WS2025) |
| Replication direction | Bidirectional | Inbound only |
| Risk if physically compromised | High — zone data exposed | Low — read-only, no write access |
| Suitable for unsecured sites? | No | Yes |
The DNS zone replica on an RODC is structurally read-only. No admin error, no rogue tool, and no attacker can modify it directly — changes only arrive through inbound AD replication from the primary DC.
When clients attempt dynamic DNS registration, the RODC transparently redirects them to the primary DC. No manual client configuration needed — the process is invisible to end users.
Branch clients get fast, local DNS responses from the RODC’s zone replica and resolver cache — no round trip to the hub DC required for known records. WAN independence for day-to-day operations.
The RODC can now validate DNSSEC signatures locally and serve signed responses to branch clients — a major security improvement over earlier server versions that required forwarding for this.
With a local zone replica and resolver cache, the RODC’s DNS service continues resolving internal and recently-queried external names even when the WAN link to the primary DC is down.
All dynamic update referral events and resolution failures are logged with expanded telemetry in Windows Server 2025 — giving you full visibility into branch DNS activity without touching the primary DC.
Here’s the complete walkthrough for enabling and configuring Read-Only DNS on your RODC in the vmorecloud.com domain, with the primary DC at 192.168.91.129.
-InstallDns flag, the role is already installed. You can skip this step and proceed directly to verification.
| Event ID | Log | What It Means |
|---|---|---|
2501 | DNS Server | Dynamic update forwarded (referral sent to primary DC) |
4013 | DNS Server | DNS Server waiting for AD replication — zone not yet loaded |
4015 | DNS Server | Critical DNS error — AD zone failed to load from RODC replica |
4523 | DNS Server | Zone loaded successfully from AD replica on RODC |
6702 | DNS Server | DNS server forwarder list updated |
6703 | DNS Server | Forwarder query failed — fallback used |
If the RODC boots before completing AD replication, the DNS zone may temporarily fail to load (Event ID 4013). This is normal and self-resolves once replication completes. If it persists beyond 15 minutes:
sc config DNS depend= NTDS). This prevents the DNS service from attempting to load zone data before AD replication has initialized — eliminating the Event ID 4013 startup race condition entirely.
A writable DNS server at a branch site is a prime target — inject a malicious record and you can redirect users to attacker-controlled resources. With Read-Only DNS, there’s no write path to exploit. Even an admin with local access to the RODC cannot inject records into the zone.
Without a local DNS server, every single query from branch clients crosses the WAN — adding latency to every application connection, login, and file access. Read-Only DNS eliminates that latency for internal names while keeping the zone data firmly under centralized control.
When the WAN link goes down, branch clients can still resolve all internal names present in the RODC’s zone replica and local cache. The branch keeps running. And because the zone is read-only, there’s no risk of split-brain DNS developing during the outage.
All DNS changes — new records, modified entries, deleted hosts — originate exclusively from the writable DC at the hub. Branch staff cannot accidentally (or maliciously) modify DNS records. Your zone data has a single, authoritative, auditable source of truth.
If an attacker gains physical access to the RODC, they inherit a read-only DNS replica they can query but not modify, AD credentials only for PRP-approved accounts, and no ability to push changes into the forest. For a DNS-focused attacker, this is a dead end.
Regulatory frameworks like PCI-DSS, ISO 27001, and NIST SP 800-53 require demonstrable controls over DNS infrastructure. Read-Only DNS on an RODC provides a clean, documentable answer: zone data at remote sites is read-only, changes are centralized, and all referral events are logged.
Read-Only DNS on Windows Server 2025 is one of those infrastructure decisions that quietly eliminates an entire category of risk. You get the performance benefits of local DNS resolution at the branch, the resilience of a locally-cached zone during WAN outages, and the security guarantees of a system that structurally cannot be used to corrupt your zone data — no matter what.
For the vmorecloud.com domain, running Read-Only DNS on BranchRODC01 with the primary DC at 192.168.91.129 as the zone source means your branch DNS infrastructure is fast, resilient, and hardened by default. Add Windows Server 2025’s new DNSSEC validation and DNS over TLS support, and you have a branch DNS stack that most enterprises would struggle to match even with much more complex setups.
Whether you’re hardening an existing RODC deployment or designing a new branch office architecture from scratch, Read-Only DNS should be a non-negotiable component of your Windows Server 2025 infrastructure strategy.
