Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Your blog category

Foxit PDF Reader 2026 (v2026.1.1.36485) Multilingual x64 is now available for download. Celebrated globally as the ultimate lightweight, high-performance alternative to bloated web-browser viewers and heavy software setups, Foxit’s free PDF reader delivers unparalleled speed and clear document visibility. The…

MuseScore Studio 4.7 has been released as the latest version of the open-source, cross-platform music notation and composition software. This release provides several engraving updates for greater control over score layout and notation. Arrowheads can now be added to text…

Canonical has added Ubuntu 26.10 to the public roadmap, confirming the codename “Stonking Stingray” and a targeted release date of October 15, 2026. This release will probably remove several features from signed GRUB builds for Secure Boot, including support for btrfs, hfsplus, xfs, and zfs as /boot filesystems,…
PostgreSQL is a robust, open-source object-relational database system that has been trusted in production environments worldwide for decades. If you’re looking to install and configure PostgreSQL on Ubuntu 26.04, this guide provides a complete walkthrough—from installing server packages and creating…
Securing your Ubuntu 26.04 system begins with one of the most critical components: how privilege escalation is managed. In this release, Canonical introduces a major change by making sudo-rs the default replacement for the traditional sudo utility. This Rust-based reimplementation…

htop 3.5 has been released as the first major upstream update in about a year, bringing interface refinements, new monitoring meters, platform-specific enhancements for Linux, macOS, and BSD systems, along with build system improvements. For those unfamiliar, htop is a…
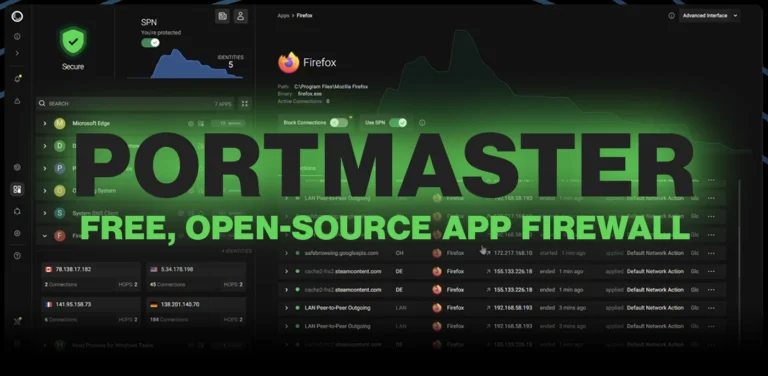
What is portmaster Every time you connect to the internet, dozens of applications on your computer are making network connections you almost certainly have no visibility into. Your browser is obvious, but what about your code editor phoning home with…

Ventoy, a popular multi-boot tool that lets you create bootable USB drives from ISO files without reformatting, has been updated to version 1.1.11. This release fixes a display issue encountered when booting Windows and WinPE ISOs in UEFI mode. In…

The Wine Project—a compatibility layer that enables Linux and macOS users to run Windows applications—has released Wine 11.6, the sixth maintenance update in the stable 11.x series. According to the release notes, this version focuses primarily on the early work…
Introduction Managing Active Directory environments often means handling machines you cannot physically reach — a remote office workstation, a laptop across the country, or a decommissioned VM sitting in a data center rack. Knowing how to remotely disjoin a computer…